Product Development

Chinmay Chandgude
How to Outsource Healthcare Product Development Without Losing Control

The U.S. healthcare outsourcing market is growing from $366.6 billion in 2025 to $662 billion by 2028, according to Black Book Research's 2025 Strategic Outlook report. That growth is not coming from organizations that want to hand something off and stop thinking about it. It is coming from founders, CTOs, and product leaders who need to build faster than their in-house team can manage, and who are figuring out, often the hard way, that outsourcing without governance is not a shortcut. It is a liability.
Most articles on this topic tell you how to pick a vendor. That is not the problem. The problem is what happens after you sign. Teams lose control not at the vendor selection stage but during the engagement: when architecture decisions get made without them, when compliance responsibility gets assumed to sit with the vendor, when the codebase becomes something only the original team can maintain, or when the IP that took months to build turns out to be contractually ambiguous.
This article is a governance playbook for the engagement itself. It covers the contract clauses that protect you before work starts, the sprint structure that keeps you informed without micromanaging, and the specific HIPAA responsibilities that cannot be delegated regardless of what your BAA says. It is written from the perspective of a team that has shipped 100+ healthcare products across 14 countries using outsourced execution pods.
For context on what teams are building with outsourced execution right now, our healthcare software development trends 2026 guide covers the full product landscape.
Why Outsourced Healthcare Projects Fail, and It Is Rarely the Code
The failure mode in outsourced healthcare development is almost never technical. The code quality might be fine. The sprint velocity might be on track. And yet, three months in, a founding team cannot answer basic questions about their own product: Why was this architectural decision made? Who owns this HIPAA risk assessment? What happens if this vendor relationship ends tomorrow?
More than 60% of healthcare providers reported project delays in 2025 due to IT talent shortages, according to industry analysis cited by TechMagic. That pressure pushes organizations to outsource quickly, often before governance structures are in place. The cost of getting it wrong is real: healthcare data breaches are the most expensive of any industry at $7.42 million on average globally, and have been the costliest sector for 14 consecutive years, according to IBM's 2025 Cost of a Data Breach Report.
The four specific ways control is lost
Most teams lose control through one of these four failure modes, and all four happen in the space between vendor selection and product delivery:
Architecture drift. The vendor makes technical decisions that are sensible in isolation but incoherent as a system. Nobody on your side reviews them in real time, and by the time the problem surfaces, unwinding it is expensive.
Compliance gaps. HIPAA and FDA responsibilities are assumed to sit with the vendor. Under HIPAA, they legally remain with you. The assumption is wrong; the liability is real.
IP ambiguity. The contract does not clearly assign ownership of the code, the clinical logic, or the data models. This surfaces at the worst possible moment: fundraising, acquisition, or FDA submission.
Sprint invisibility. You receive a weekly status report but cannot independently verify what was built, why certain decisions were made, or whether the product is still buildable by a team other than the one currently working on it.
All four are governance failures, not vendor failures. That distinction matters because it means the solution is in your control.
What "Keeping Control" Actually Means in a Healthcare Outsourcing Engagement
Control in healthcare product outsourcing means ensuring four specific things remain in your hands throughout the engagement, regardless of which vendor is doing the work. It is not micromanaging tickets or sitting in every standup.
The four dimensions of control
Dimension | What it means in practice | The test |
Architecture ownership | You can describe every major technical decision and why it was made | Could a new engineer read your architecture docs and understand the system? |
IP and code ownership | Code, clinical logic, data schemas, and AI model weights belong to you at every stage | Is IP assigned at contract signing, or only at handoff? |
Compliance accountability | You know which HIPAA decisions have been made, which are pending, and who made them | Do you have a compliance decision log? |
Sprint visibility | You can answer at any point: what was built, what decisions were made, is the build continuable? | If your vendor left tomorrow, how many weeks to continue building? |
A useful test to apply right now: if the vendor relationship ended today, how many weeks would it take your team to continue building without them? If the answer is months, the vendor has more control over the engagement than you do.
Before You Sign: The Contract Clauses That Protect Your Control
The four contract clauses that protect control in a healthcare outsourcing engagement are consistently the ones that receive the least attention during negotiation. Most contracts are negotiated on price, timeline, and scope. These four are the ones that matter when something goes wrong. Ask your legal team to verify and adapt each for your specific situation.
1. IP assignment at contract signing, not at project close
There are two structures to know:
Work-for-hire: All IP created during the engagement belongs to you immediately, from the first line of code.
License-back: The vendor retains ownership and licenses the work to you. This is the default in many standard outsourcing contracts.
For healthcare products, work-for-hire is not optional. FDA submissions reference specific product architecture. Future acqui-hire scenarios assume clean IP ownership. Any ambiguity here costs significantly more to resolve after the fact than it would have cost to get right in the contract.
2. BAA scope that covers all subcontractors
A Business Associate Agreement with your primary vendor is not sufficient if that vendor uses subcontractors who will touch protected health information. The HHS Business Associate guidance is explicit: the chain of HIPAA accountability must extend to every subcontractor who handles PHI.
Before work starts, require the following:
A complete subcontractor list from the vendor
Confirmation that BAAs are in place for every subcontractor on that list
A contractual obligation for the vendor to notify you before adding new subcontractors who will access PHI
A gap in that chain is a gap in your compliance posture and under HIPAA, that liability is yours.
3. Architecture documentation as a contractual deliverable
Architecture documentation is typically treated as a post-project artifact that the vendor produces at the end of the engagement if time allows. Make it a required milestone deliverable instead:
After the first sprint: Initial system design documented
After each major technical decision: Architecture Decision Records (ADRs) produced — brief documents capturing the choice, alternatives considered, and the reasoning
At engagement close: Full system documentation delivered in a format your team owns
ADRs should be a required output at each sprint, not an optional courtesy at the end.
4. A 30-day knowledge transfer obligation on exit
If the engagement ends for any reason, the vendor must participate in a structured 30-day knowledge transfer. This clause should require:
Documented handoff of all credentials and system access
Complete architecture documentation in a format your team controls
A walkthrough of each major system component
A code review session covering non-obvious implementation decisions
Without this clause, you depend entirely on the vendor's goodwill when the relationship ends. Goodwill is less reliable than a contractual obligation.
Want the full checklist of contract clauses Latent requires before starting any healthcare engagement? Book a free 30-minute call and we will walk through it with you. Book a free call →
How to Structure Sprint Governance So You See Everything Without Slowing the Build
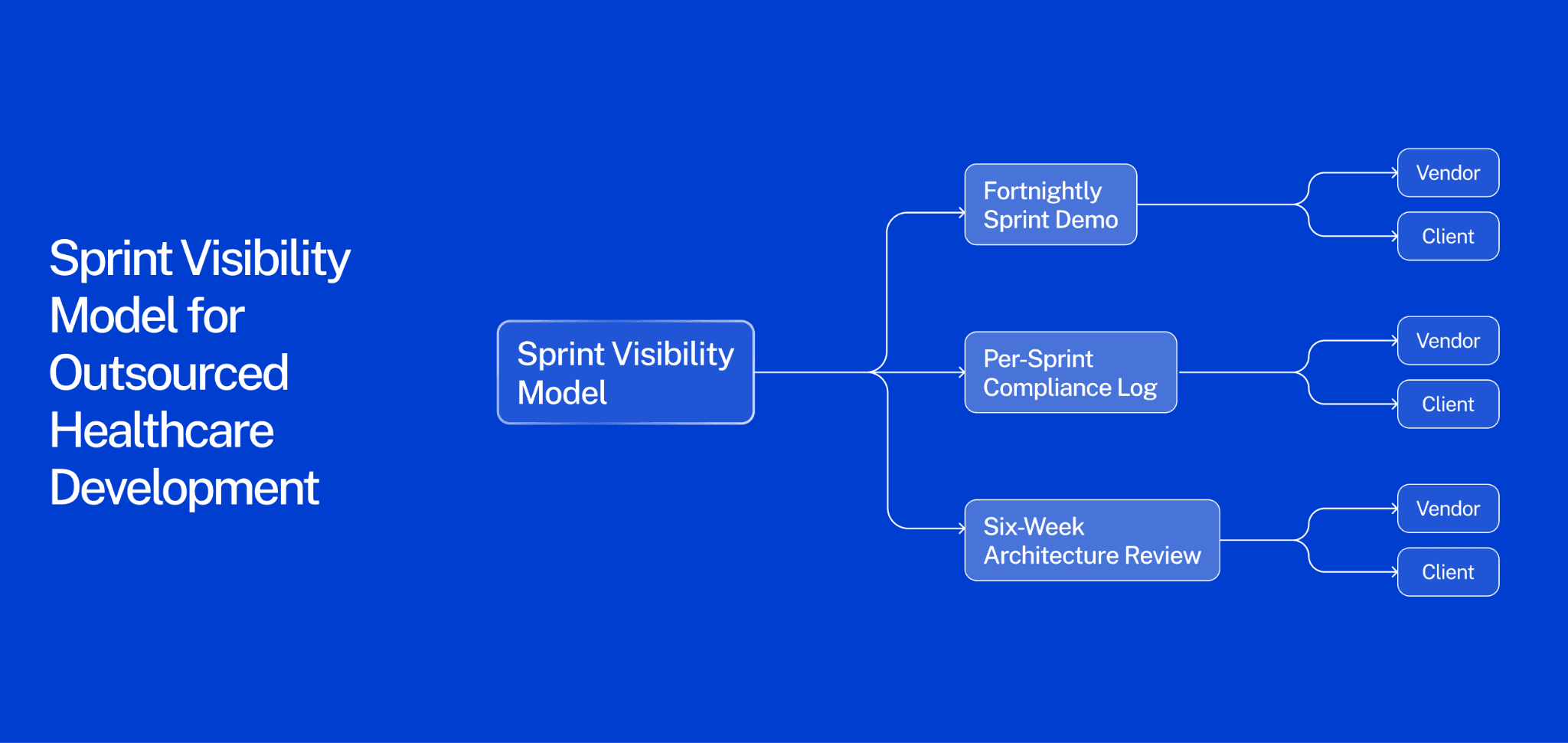
The most reliable way to maintain control throughout an outsourced healthcare build is a three-layer visibility model: a fortnightly sprint demo, a per-sprint compliance log, and a six-week architecture review.
The most common source of lost control is not a bad vendor. It is a good vendor building something the client cannot independently verify. Weekly status reports tell you what the vendor did. They do not tell you whether the product is still yours.
Layer 1: Fortnightly sprint demo
Every two weeks, your product owner attends a live walkthrough of what was built. Not a status update email — a working demo where decisions get made. This is how product direction stays with you.
If you are only reading updates rather than seeing a working product, sprint decisions drift toward what the vendor finds technically convenient rather than what you need commercially. A fortnightly demo costs one hour. Losing product direction costs months.
Layer 2: Per-sprint compliance log
Every sprint should produce a brief compliance decision log. The vendor documents:
What PHI was handled during the sprint
What security or access control decisions were made
What HIPAA or FDA considerations came up and how they were resolved
What open compliance questions require your input before the next sprint
This does not require a compliance officer on every sprint call. It requires the vendor to fill in a shared document that your team reviews. Healthcare is the most expensive data breach industry for a reason: compliance decisions made casually during development become liability at launch.
Layer 3: Six-week architecture review
Every six weeks, a senior engineer on your side or a trusted third party reviews the current state of the codebase against the architecture documentation. The question is not "is the code good?" It is: is this codebase still buildable by a team other than the one currently working on it?
This is the bus test applied practically. If the answer is no, it gets resolved in the next sprint — not at handoff, when it is expensive to fix.
Tools that support this model without adding overhead
Project management: Jira or Linear with full client access, not a vendor-curated view
Compliance log: Notion or Confluence document owned and editable by your team
Architecture docs: Format your team controls and can update independently
For product teams evaluating how AI and compliance decisions interact across development sprints, our guide to AI in healthcare product development 2026 covers the governance architecture decisions in detail.
Compliance Ownership: The HIPAA and FDA Responsibilities That Cannot Be Delegated
Under HIPAA, the covered entity remains accountable for compliance even when a Business Associate Agreement is signed. Signing a BAA transfers certain contractual obligations to the vendor. It does not transfer regulatory accountability.
According to HHS OCR guidance, a covered entity can be held liable for a vendor's PHI breach if it failed to conduct adequate due diligence before engagement or failed to monitor vendor compliance throughout the relationship. This distinction determines what you must own internally regardless of your vendor arrangement.
What stays with you — non-delegable responsibilities
These four responsibilities cannot be handed off to the vendor, regardless of BAA scope:
HIPAA risk assessment. The formal evaluation of risks to PHI across your system is the covered entity's responsibility to own, conduct, and update. Your vendor can provide technical inputs; they cannot author the assessment on your behalf.
PHI classification decisions. The decision to classify a data type as protected health information sits with you. If a vendor advises that a data type is not PHI and OCR later determines otherwise, the liability is yours.
Security rule policy decisions. Which safeguards to implement, how to configure access controls, how to handle audit logs — these policy decisions remain the covered entity's responsibility to direct, even when a vendor implements them technically.
FDA 510(k) submissions. If your product is a Software as a Medical Device, the submission references specific product architecture and decision-making logic. If the vendor owns key IP or architectural decisions, the submission may be compromised.
What can be delegated with a properly scoped BAA
These are engineering tasks vendors handle routinely. The policy decisions that govern them stay with you; the technical execution can be outsourced:
Encryption standards and implementation
Access control architecture and role-based permission systems
Audit log generation and storage
Intrusion detection and monitoring infrastructure
For teams navigating compliance requirements across healthcare software categories, our guide to key requirements for building mental health software covers the compliance architecture decisions that apply broadly across healthcare products.
IP Protection in Healthcare Outsourcing: What Founders Consistently Get Wrong
Healthcare IP is not just source code. The clinical logic, data schemas, architectural decisions, and AI training data that define your product are all IP — and most outsourcing contracts only protect the first of these four.
Almost every outsourcing IP clause covers source code. Almost none explicitly addresses everything else. The assets beyond source code are often the ones that represent your actual competitive differentiation, and the ones that surface as problems at fundraising, FDA submission, or acquisition.
The four healthcare IP assets that require explicit contract protection
1. Source code — the obvious one, and most contracts do address it. Address it specifically: work-for-hire with assignment of all copyrights, not a license. Also confirm that no third-party proprietary libraries are embedded in your codebase without a license that permits your use case.
2. Architecture documentation — the one most teams miss. A vendor who documents system architecture in their own internal tools and does not transfer that documentation to you effectively owns the institutional knowledge of how your system works, even if you technically own the code.
3. Clinical logic and decision trees — your actual product differentiation. If your product recommends a treatment pathway, flags a risk condition, or surfaces a clinical insight, the rules and logic behind that decision are your competitive moat. They must be explicitly assigned in the contract; they will not automatically transfer with the source code.
4. AI training data and model weights — the newest and most legally unsettled IP category. For any machine learning component, confirm in writing:
Who owns the training data used to build the model
Who owns the model weights produced during training
Whether the vendor retains any right to use your data to improve models deployed for other clients
This last point is frequently buried in standard vendor terms of service rather than in the outsourcing contract, and it catches teams off guard consistently.
Pre-signing IP checklist
Ask the vendor directly before signing:
Do you use any proprietary libraries or frameworks in your standard stack?
Are any open-source components under copyleft licenses (such as GPL) that would affect our ability to distribute the product?
Do your standard engagement terms include any rights to use client data or work product for your own internal purposes, model training, or product improvement?
For teams evaluating how IP decisions affect healthcare app development economics, our guide to healthcare app development cost covers how these choices affect long-term build cost.
The Managed Pod Model: How Latent Structures Outsourced Healthcare Builds
The governance problems described in this article are predictable and solvable — but only if governance is built into the engagement structure from day one, not retrofitted after problems emerge.
Treating outsourced healthcare development as a standard vendor relationship produces the standard failure modes. Treating it as an embedded execution partnership with built-in visibility structures produces a product you own and can continue building independently.
What the managed pod model does differently
Standard outsourcing | Latent managed pod |
IP assigned at project close | IP assigned at contract signing: code, architecture docs, clinical logic, AI training data |
Compliance is the vendor's responsibility | Compliance decision log produced every sprint, owned by the client |
Architecture reviewed at end of engagement | Architecture reviewed every six weeks against living documentation |
Client receives a curated status report | Client has full access to the project management environment |
Exit terms determined at end | 30-day knowledge transfer clause in the contract from the start |
Healthcare IT outsourcing is on track to grow from $60.6 billion in 2025 to $117.1 billion by 2035, according to Future Market Insights. The teams that navigate that growth well are the ones that treated governance as a first-order product design requirement.
Latent's managed pods deliver MVPs in 8–14 weeks with compliance, architecture ownership, and sprint visibility built in from day one. If you want to see how this works for a product like yours, book a free discovery sprint. We will scope the build, map the compliance decisions, and give you a clear architecture direction before you commit long-term.
Frequently Asked Questions
How do you outsource healthcare product development without losing control?
Establish four governance mechanisms before the engagement starts: an IP assignment clause (work-for-hire, covering code, architecture docs, clinical logic, and AI training data), a BAA that explicitly covers all subcontractors who will touch PHI, a sprint governance model with fortnightly demos and a per-sprint compliance decision log, and an architecture documentation requirement with a 30-day knowledge transfer obligation on exit. These four mechanisms directly address the four specific failure modes: IP ambiguity, compliance gaps, sprint invisibility, and architecture drift.
What should a healthcare software outsourcing contract include?
At minimum: a work-for-hire IP assignment covering all product assets (not just source code), a BAA with subcontractor flow-down requirements, architecture documentation as a milestone deliverable (not a post-project artifact), a per-sprint compliance decision log requirement, and a structured exit clause with a 30-day knowledge transfer obligation. Standard outsourcing contracts typically include only a fraction of these protections. Ask your legal team to verify each clause for your specific regulatory context before signing.
Who is responsible for HIPAA compliance in an outsourced healthcare project?
The covered entity remains accountable under HIPAA even when a BAA is in place. According to HHS OCR, a covered entity can be held liable for a vendor's PHI breach if it failed to conduct adequate due diligence or failed to monitor vendor compliance throughout the relationship. The BAA shifts certain contractual obligations to the vendor; it does not transfer regulatory accountability. Responsibilities that remain with the covered entity regardless of vendor arrangement include: the HIPAA risk assessment, PHI classification decisions, and security rule policy decisions.
How much does it cost to outsource healthcare product development?
MVPs for healthcare software typically range from $40,000 to $150,000 depending on scope, compliance requirements, and EHR integration complexity. Enterprise-grade products with full compliance infrastructure, EHR write-back, and clinical validation documentation typically cost $500,000 or more. Managed pod models generally reduce total cost by 30–60% compared to building equivalent in-house capacity by eliminating recruitment, HR overhead, and infrastructure costs. Governance infrastructure adds minimal cost when built in from the start; retrofitting it after problems emerge costs significantly more.
What is the difference between outsourcing healthcare software and using a managed pod?
Traditional outsourcing hands a brief to a vendor who builds to spec, with periodic updates and a handoff at the end. A managed pod embeds governance into the engagement structure from day one: sprint visibility, compliance checkpoints, architecture ownership, and IP assignment are the default operating model, not optional additions. For healthcare products specifically, where compliance accountability stays with the covered entity regardless of vendor agreements, this structural difference determines whether the product is deployable or a liability when it ships.
The U.S. healthcare outsourcing market is growing from $366.6 billion in 2025 to $662 billion by 2028, according to Black Book Research's 2025 Strategic Outlook report. That growth is not coming from organizations that want to hand something off and stop thinking about it. It is coming from founders, CTOs, and product leaders who need to build faster than their in-house team can manage, and who are figuring out, often the hard way, that outsourcing without governance is not a shortcut. It is a liability.
Most articles on this topic tell you how to pick a vendor. That is not the problem. The problem is what happens after you sign. Teams lose control not at the vendor selection stage but during the engagement: when architecture decisions get made without them, when compliance responsibility gets assumed to sit with the vendor, when the codebase becomes something only the original team can maintain, or when the IP that took months to build turns out to be contractually ambiguous.
This article is a governance playbook for the engagement itself. It covers the contract clauses that protect you before work starts, the sprint structure that keeps you informed without micromanaging, and the specific HIPAA responsibilities that cannot be delegated regardless of what your BAA says. It is written from the perspective of a team that has shipped 100+ healthcare products across 14 countries using outsourced execution pods.
For context on what teams are building with outsourced execution right now, our healthcare software development trends 2026 guide covers the full product landscape.
Why Outsourced Healthcare Projects Fail, and It Is Rarely the Code
The failure mode in outsourced healthcare development is almost never technical. The code quality might be fine. The sprint velocity might be on track. And yet, three months in, a founding team cannot answer basic questions about their own product: Why was this architectural decision made? Who owns this HIPAA risk assessment? What happens if this vendor relationship ends tomorrow?
More than 60% of healthcare providers reported project delays in 2025 due to IT talent shortages, according to industry analysis cited by TechMagic. That pressure pushes organizations to outsource quickly, often before governance structures are in place. The cost of getting it wrong is real: healthcare data breaches are the most expensive of any industry at $7.42 million on average globally, and have been the costliest sector for 14 consecutive years, according to IBM's 2025 Cost of a Data Breach Report.
The four specific ways control is lost
Most teams lose control through one of these four failure modes, and all four happen in the space between vendor selection and product delivery:
Architecture drift. The vendor makes technical decisions that are sensible in isolation but incoherent as a system. Nobody on your side reviews them in real time, and by the time the problem surfaces, unwinding it is expensive.
Compliance gaps. HIPAA and FDA responsibilities are assumed to sit with the vendor. Under HIPAA, they legally remain with you. The assumption is wrong; the liability is real.
IP ambiguity. The contract does not clearly assign ownership of the code, the clinical logic, or the data models. This surfaces at the worst possible moment: fundraising, acquisition, or FDA submission.
Sprint invisibility. You receive a weekly status report but cannot independently verify what was built, why certain decisions were made, or whether the product is still buildable by a team other than the one currently working on it.
All four are governance failures, not vendor failures. That distinction matters because it means the solution is in your control.
What "Keeping Control" Actually Means in a Healthcare Outsourcing Engagement
Control in healthcare product outsourcing means ensuring four specific things remain in your hands throughout the engagement, regardless of which vendor is doing the work. It is not micromanaging tickets or sitting in every standup.
The four dimensions of control
Dimension | What it means in practice | The test |
Architecture ownership | You can describe every major technical decision and why it was made | Could a new engineer read your architecture docs and understand the system? |
IP and code ownership | Code, clinical logic, data schemas, and AI model weights belong to you at every stage | Is IP assigned at contract signing, or only at handoff? |
Compliance accountability | You know which HIPAA decisions have been made, which are pending, and who made them | Do you have a compliance decision log? |
Sprint visibility | You can answer at any point: what was built, what decisions were made, is the build continuable? | If your vendor left tomorrow, how many weeks to continue building? |
A useful test to apply right now: if the vendor relationship ended today, how many weeks would it take your team to continue building without them? If the answer is months, the vendor has more control over the engagement than you do.
Before You Sign: The Contract Clauses That Protect Your Control
The four contract clauses that protect control in a healthcare outsourcing engagement are consistently the ones that receive the least attention during negotiation. Most contracts are negotiated on price, timeline, and scope. These four are the ones that matter when something goes wrong. Ask your legal team to verify and adapt each for your specific situation.
1. IP assignment at contract signing, not at project close
There are two structures to know:
Work-for-hire: All IP created during the engagement belongs to you immediately, from the first line of code.
License-back: The vendor retains ownership and licenses the work to you. This is the default in many standard outsourcing contracts.
For healthcare products, work-for-hire is not optional. FDA submissions reference specific product architecture. Future acqui-hire scenarios assume clean IP ownership. Any ambiguity here costs significantly more to resolve after the fact than it would have cost to get right in the contract.
2. BAA scope that covers all subcontractors
A Business Associate Agreement with your primary vendor is not sufficient if that vendor uses subcontractors who will touch protected health information. The HHS Business Associate guidance is explicit: the chain of HIPAA accountability must extend to every subcontractor who handles PHI.
Before work starts, require the following:
A complete subcontractor list from the vendor
Confirmation that BAAs are in place for every subcontractor on that list
A contractual obligation for the vendor to notify you before adding new subcontractors who will access PHI
A gap in that chain is a gap in your compliance posture and under HIPAA, that liability is yours.
3. Architecture documentation as a contractual deliverable
Architecture documentation is typically treated as a post-project artifact that the vendor produces at the end of the engagement if time allows. Make it a required milestone deliverable instead:
After the first sprint: Initial system design documented
After each major technical decision: Architecture Decision Records (ADRs) produced — brief documents capturing the choice, alternatives considered, and the reasoning
At engagement close: Full system documentation delivered in a format your team owns
ADRs should be a required output at each sprint, not an optional courtesy at the end.
4. A 30-day knowledge transfer obligation on exit
If the engagement ends for any reason, the vendor must participate in a structured 30-day knowledge transfer. This clause should require:
Documented handoff of all credentials and system access
Complete architecture documentation in a format your team controls
A walkthrough of each major system component
A code review session covering non-obvious implementation decisions
Without this clause, you depend entirely on the vendor's goodwill when the relationship ends. Goodwill is less reliable than a contractual obligation.
Want the full checklist of contract clauses Latent requires before starting any healthcare engagement? Book a free 30-minute call and we will walk through it with you. Book a free call →
How to Structure Sprint Governance So You See Everything Without Slowing the Build
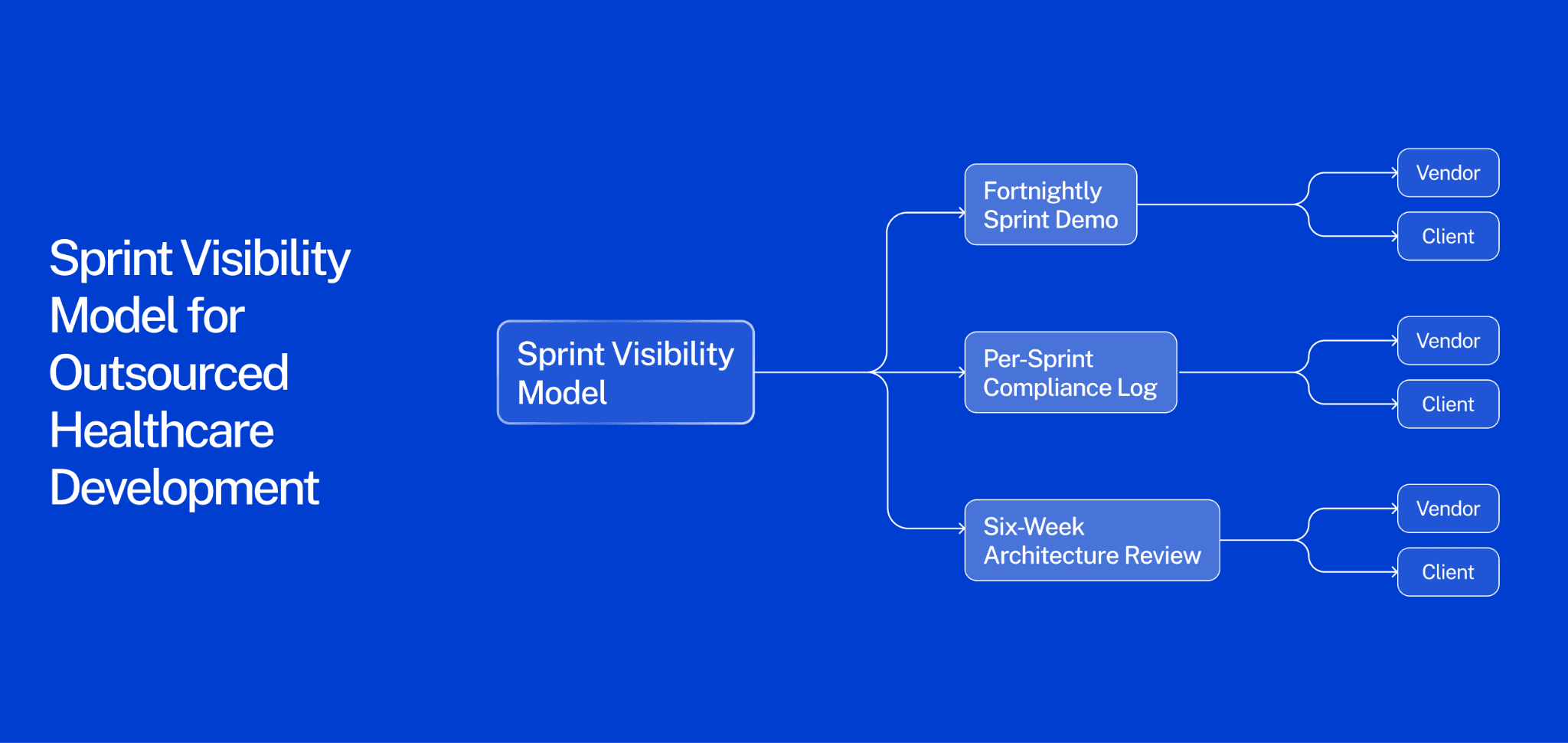
The most reliable way to maintain control throughout an outsourced healthcare build is a three-layer visibility model: a fortnightly sprint demo, a per-sprint compliance log, and a six-week architecture review.
The most common source of lost control is not a bad vendor. It is a good vendor building something the client cannot independently verify. Weekly status reports tell you what the vendor did. They do not tell you whether the product is still yours.
Layer 1: Fortnightly sprint demo
Every two weeks, your product owner attends a live walkthrough of what was built. Not a status update email — a working demo where decisions get made. This is how product direction stays with you.
If you are only reading updates rather than seeing a working product, sprint decisions drift toward what the vendor finds technically convenient rather than what you need commercially. A fortnightly demo costs one hour. Losing product direction costs months.
Layer 2: Per-sprint compliance log
Every sprint should produce a brief compliance decision log. The vendor documents:
What PHI was handled during the sprint
What security or access control decisions were made
What HIPAA or FDA considerations came up and how they were resolved
What open compliance questions require your input before the next sprint
This does not require a compliance officer on every sprint call. It requires the vendor to fill in a shared document that your team reviews. Healthcare is the most expensive data breach industry for a reason: compliance decisions made casually during development become liability at launch.
Layer 3: Six-week architecture review
Every six weeks, a senior engineer on your side or a trusted third party reviews the current state of the codebase against the architecture documentation. The question is not "is the code good?" It is: is this codebase still buildable by a team other than the one currently working on it?
This is the bus test applied practically. If the answer is no, it gets resolved in the next sprint — not at handoff, when it is expensive to fix.
Tools that support this model without adding overhead
Project management: Jira or Linear with full client access, not a vendor-curated view
Compliance log: Notion or Confluence document owned and editable by your team
Architecture docs: Format your team controls and can update independently
For product teams evaluating how AI and compliance decisions interact across development sprints, our guide to AI in healthcare product development 2026 covers the governance architecture decisions in detail.
Compliance Ownership: The HIPAA and FDA Responsibilities That Cannot Be Delegated
Under HIPAA, the covered entity remains accountable for compliance even when a Business Associate Agreement is signed. Signing a BAA transfers certain contractual obligations to the vendor. It does not transfer regulatory accountability.
According to HHS OCR guidance, a covered entity can be held liable for a vendor's PHI breach if it failed to conduct adequate due diligence before engagement or failed to monitor vendor compliance throughout the relationship. This distinction determines what you must own internally regardless of your vendor arrangement.
What stays with you — non-delegable responsibilities
These four responsibilities cannot be handed off to the vendor, regardless of BAA scope:
HIPAA risk assessment. The formal evaluation of risks to PHI across your system is the covered entity's responsibility to own, conduct, and update. Your vendor can provide technical inputs; they cannot author the assessment on your behalf.
PHI classification decisions. The decision to classify a data type as protected health information sits with you. If a vendor advises that a data type is not PHI and OCR later determines otherwise, the liability is yours.
Security rule policy decisions. Which safeguards to implement, how to configure access controls, how to handle audit logs — these policy decisions remain the covered entity's responsibility to direct, even when a vendor implements them technically.
FDA 510(k) submissions. If your product is a Software as a Medical Device, the submission references specific product architecture and decision-making logic. If the vendor owns key IP or architectural decisions, the submission may be compromised.
What can be delegated with a properly scoped BAA
These are engineering tasks vendors handle routinely. The policy decisions that govern them stay with you; the technical execution can be outsourced:
Encryption standards and implementation
Access control architecture and role-based permission systems
Audit log generation and storage
Intrusion detection and monitoring infrastructure
For teams navigating compliance requirements across healthcare software categories, our guide to key requirements for building mental health software covers the compliance architecture decisions that apply broadly across healthcare products.
IP Protection in Healthcare Outsourcing: What Founders Consistently Get Wrong
Healthcare IP is not just source code. The clinical logic, data schemas, architectural decisions, and AI training data that define your product are all IP — and most outsourcing contracts only protect the first of these four.
Almost every outsourcing IP clause covers source code. Almost none explicitly addresses everything else. The assets beyond source code are often the ones that represent your actual competitive differentiation, and the ones that surface as problems at fundraising, FDA submission, or acquisition.
The four healthcare IP assets that require explicit contract protection
1. Source code — the obvious one, and most contracts do address it. Address it specifically: work-for-hire with assignment of all copyrights, not a license. Also confirm that no third-party proprietary libraries are embedded in your codebase without a license that permits your use case.
2. Architecture documentation — the one most teams miss. A vendor who documents system architecture in their own internal tools and does not transfer that documentation to you effectively owns the institutional knowledge of how your system works, even if you technically own the code.
3. Clinical logic and decision trees — your actual product differentiation. If your product recommends a treatment pathway, flags a risk condition, or surfaces a clinical insight, the rules and logic behind that decision are your competitive moat. They must be explicitly assigned in the contract; they will not automatically transfer with the source code.
4. AI training data and model weights — the newest and most legally unsettled IP category. For any machine learning component, confirm in writing:
Who owns the training data used to build the model
Who owns the model weights produced during training
Whether the vendor retains any right to use your data to improve models deployed for other clients
This last point is frequently buried in standard vendor terms of service rather than in the outsourcing contract, and it catches teams off guard consistently.
Pre-signing IP checklist
Ask the vendor directly before signing:
Do you use any proprietary libraries or frameworks in your standard stack?
Are any open-source components under copyleft licenses (such as GPL) that would affect our ability to distribute the product?
Do your standard engagement terms include any rights to use client data or work product for your own internal purposes, model training, or product improvement?
For teams evaluating how IP decisions affect healthcare app development economics, our guide to healthcare app development cost covers how these choices affect long-term build cost.
The Managed Pod Model: How Latent Structures Outsourced Healthcare Builds
The governance problems described in this article are predictable and solvable — but only if governance is built into the engagement structure from day one, not retrofitted after problems emerge.
Treating outsourced healthcare development as a standard vendor relationship produces the standard failure modes. Treating it as an embedded execution partnership with built-in visibility structures produces a product you own and can continue building independently.
What the managed pod model does differently
Standard outsourcing | Latent managed pod |
IP assigned at project close | IP assigned at contract signing: code, architecture docs, clinical logic, AI training data |
Compliance is the vendor's responsibility | Compliance decision log produced every sprint, owned by the client |
Architecture reviewed at end of engagement | Architecture reviewed every six weeks against living documentation |
Client receives a curated status report | Client has full access to the project management environment |
Exit terms determined at end | 30-day knowledge transfer clause in the contract from the start |
Healthcare IT outsourcing is on track to grow from $60.6 billion in 2025 to $117.1 billion by 2035, according to Future Market Insights. The teams that navigate that growth well are the ones that treated governance as a first-order product design requirement.
Latent's managed pods deliver MVPs in 8–14 weeks with compliance, architecture ownership, and sprint visibility built in from day one. If you want to see how this works for a product like yours, book a free discovery sprint. We will scope the build, map the compliance decisions, and give you a clear architecture direction before you commit long-term.
Frequently Asked Questions
How do you outsource healthcare product development without losing control?
Establish four governance mechanisms before the engagement starts: an IP assignment clause (work-for-hire, covering code, architecture docs, clinical logic, and AI training data), a BAA that explicitly covers all subcontractors who will touch PHI, a sprint governance model with fortnightly demos and a per-sprint compliance decision log, and an architecture documentation requirement with a 30-day knowledge transfer obligation on exit. These four mechanisms directly address the four specific failure modes: IP ambiguity, compliance gaps, sprint invisibility, and architecture drift.
What should a healthcare software outsourcing contract include?
At minimum: a work-for-hire IP assignment covering all product assets (not just source code), a BAA with subcontractor flow-down requirements, architecture documentation as a milestone deliverable (not a post-project artifact), a per-sprint compliance decision log requirement, and a structured exit clause with a 30-day knowledge transfer obligation. Standard outsourcing contracts typically include only a fraction of these protections. Ask your legal team to verify each clause for your specific regulatory context before signing.
Who is responsible for HIPAA compliance in an outsourced healthcare project?
The covered entity remains accountable under HIPAA even when a BAA is in place. According to HHS OCR, a covered entity can be held liable for a vendor's PHI breach if it failed to conduct adequate due diligence or failed to monitor vendor compliance throughout the relationship. The BAA shifts certain contractual obligations to the vendor; it does not transfer regulatory accountability. Responsibilities that remain with the covered entity regardless of vendor arrangement include: the HIPAA risk assessment, PHI classification decisions, and security rule policy decisions.
How much does it cost to outsource healthcare product development?
MVPs for healthcare software typically range from $40,000 to $150,000 depending on scope, compliance requirements, and EHR integration complexity. Enterprise-grade products with full compliance infrastructure, EHR write-back, and clinical validation documentation typically cost $500,000 or more. Managed pod models generally reduce total cost by 30–60% compared to building equivalent in-house capacity by eliminating recruitment, HR overhead, and infrastructure costs. Governance infrastructure adds minimal cost when built in from the start; retrofitting it after problems emerge costs significantly more.
What is the difference between outsourcing healthcare software and using a managed pod?
Traditional outsourcing hands a brief to a vendor who builds to spec, with periodic updates and a handoff at the end. A managed pod embeds governance into the engagement structure from day one: sprint visibility, compliance checkpoints, architecture ownership, and IP assignment are the default operating model, not optional additions. For healthcare products specifically, where compliance accountability stays with the covered entity regardless of vendor agreements, this structural difference determines whether the product is deployable or a liability when it ships.

Chinmay Chandgude is a partner at Latent with over 9 years of experience in building custom digital platforms for healthcare and finance sectors. He focuses on creating scalable and secure web and mobile applications to drive technological transformation. Based in Pune, India, Chinmay is passionate about delivering user-centric solutions that improve efficiency and reduce costs.
Related Posts
Free MVP Architecture
Share your product idea — we'll design your MVP architecture for free, no commitment required. If it's a good fit, we'll show you what building it looks like.



